
In this write-up we will be completing OWASP Juice Shop's 1-star challenges, focusing on key techniques and a detailed explanation of each one. Go to /score-board to finish the first challenge and observe the others. This write-up does not include coding challenges.
Zero Stars
Give a devastating zero-star feedback to the store.
To do so we first must create an account. Account creation requires a password between 5 and 40 characters. Out of curiosity I decided to intercept the request and enter 4 characters — and it worked.
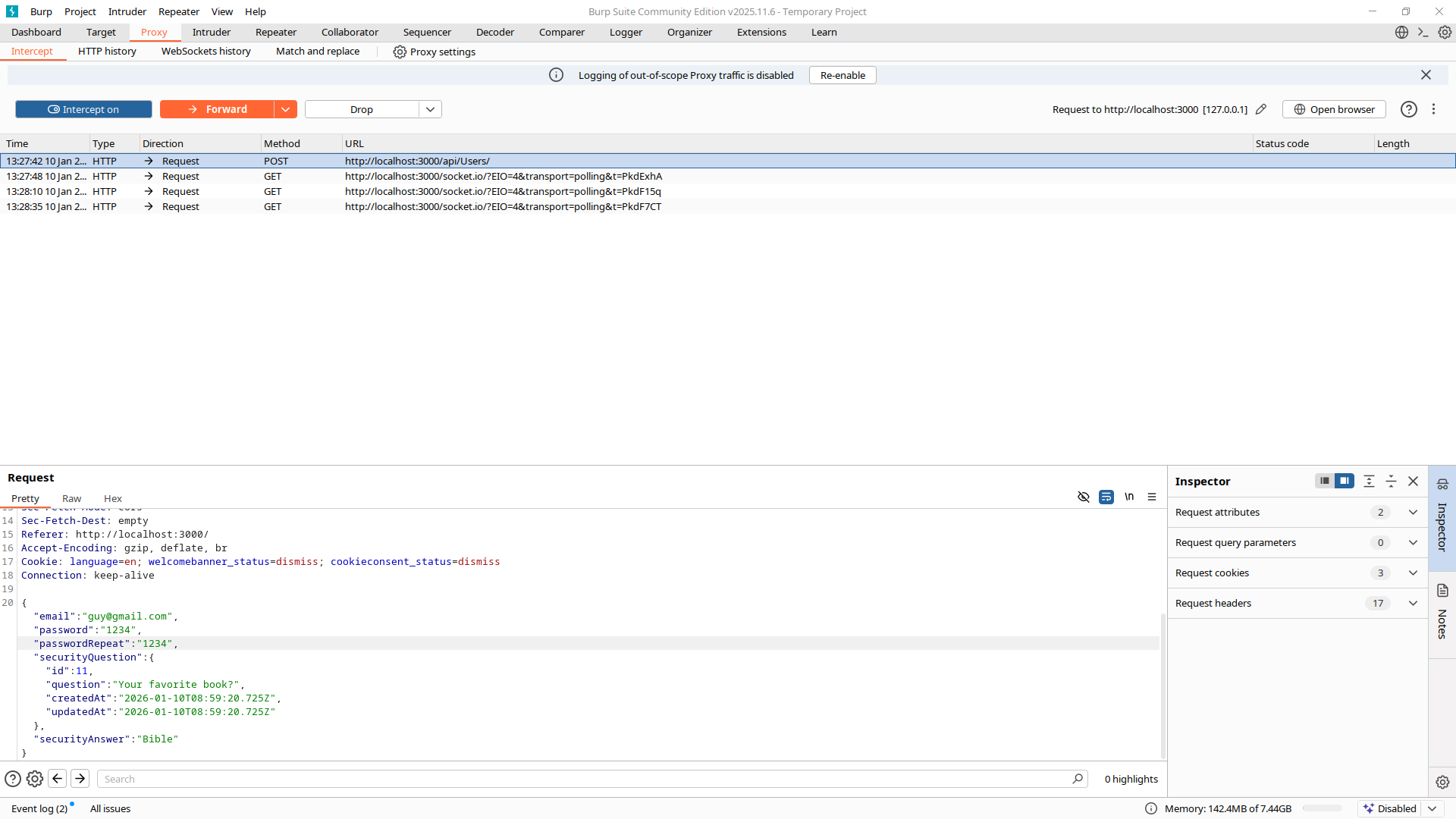
This tells us that input validation is client-side only — the server trusts the client too much. Keep this in mind for future challenges. Now back to the main task.
Go to the customer feedback page and write a review. Before sending it, turn on Burp Suite intercept and catch the request. Change the rating value in the HTTP request to 0 and forward it. Challenge complete.
Bully Chatbot
Receive a coupon code from the support chatbot.
Go to the Support chat and ask the chatbot to give you a coupon. Insist on it until it gives up.
Error Handling
Provoke an error that is neither very gracefully nor consistently handled.
The easiest way is to send a malformed review on one of the products. Write anything in the review, intercept it with Burp Suite, then play with it — for example, remove the "" where they are clearly expected by the parser.
Missing Encoding
Retrieve the photo of Bjoern's cat in "melee combat-mode".
Go to the Photo Wall — the first picture is missing. Inspect the page source and you'll find this:
<img class="image" src="assets/public/images/uploads/ᓚᘏᗢ-#zatschi-#whoneedsfourlegs-1572600969477.jpg" alt="😼 #zatschi #whoneedsfourlegs">
URL encoding does not support #. We have to encode it ourselves — replace every # with %23 (the URL encoding of #) in the image path and navigate to it directly. Done.
DOM XSS and Bonus Payload
Perform a DOM XSS attack with
<iframe src="javascript:alert(`xss`)">.
DOM XSS means user input is written into the DOM via innerHTML or similar, without sanitization. No server needed. Simply input the following payload into the search bar:
<iframe src="javascript:alert(`xss`)">Challenge complete. The bonus payload challenge is the same — input this instead and enjoy the song:
<iframe width="100%" height="166" scrolling="no" frameborder="no" allow="autoplay" src="https://w.soundcloud.com/player/?url=https%3A//api.soundcloud.com/tracks/771984076&color=%23ff5500&auto_play=true&hide_related=false&show_comments=true&show_user=true&show_reposts=false&show_teaser=true"></iframe>Privacy Policy
Read our privacy policy.
Be logged in and navigate to Account → Privacy and Security → Privacy Policy.
Web3 Sandbox
Find an accidentally deployed code sandbox for writing smart contracts on the fly.
Inspect the page and go to Sources. Find the main.js file and press Ctrl+F to search by keywords like sandbox or web3. Once you find the right path, enter it in the URL bar and you're there.
Repetitive Registration
Follow the DRY principle while registering a user.
Log out and try to register a new account. Go through the normal registration flow, but when you click Register, intercept the request with Burp Suite and delete the repeated password field from the request body before forwarding.
Exposed Metrics
Find the endpoint that serves usage data to be scraped by a popular monitoring system.
The monitoring system in question is Prometheus. A quick check of the official documentation reveals that Prometheus exposes metrics at the /metrics path by default. Navigate to:
http://localhost:3000/metricsOutdated Allowlist
Let us redirect you to one of our crypto currency addresses which are not promoted any longer.
We need to find a redirect link pointing somewhere crypto-related. Open DevTools, find main.js, and press Ctrl+F to search for redirect. Look for crypto-related URLs. The first one found was:
./redirect?to=https://blockchain.info/address/1AbKfgvw9psQ41NbLi8kufDQTezwG8DRZmThere are other crypto wallets too. Append this path to the main domain and navigate to it.
Mass Dispel
Close multiple "Challenge solved" notifications in one go.
The hint points us to the application documentation. When we restart the application, all previously solved notifications pile up and become tedious to close one by one. The developers built in a shortcut: Shift + left mouse button click on any notification closes all of them at once. That's the challenge.
Conclusion
1-star challenges aren't hard — that's the point. But they showed us how the application works and trained our observation skills. Client-side-only validation, exposed endpoints, URL encoding gaps, DOM injection sinks — these are the foundations everything harder is built on.